Cybercriminals Now Using Barcode Security Threat
Here’s the scenario: While innocently scanning a barcode, your desktop is wiped out. The computer is transformed into an open door for cybersecurity attacks. This is exactly what happened to our Director of Engineering, Gene Anderson. He called it his “Aha!” moment because, in that instant, he realized that encoded malicious info can indeed be hidden within a 2D barcode.
Why is Data Security An Issue Now?
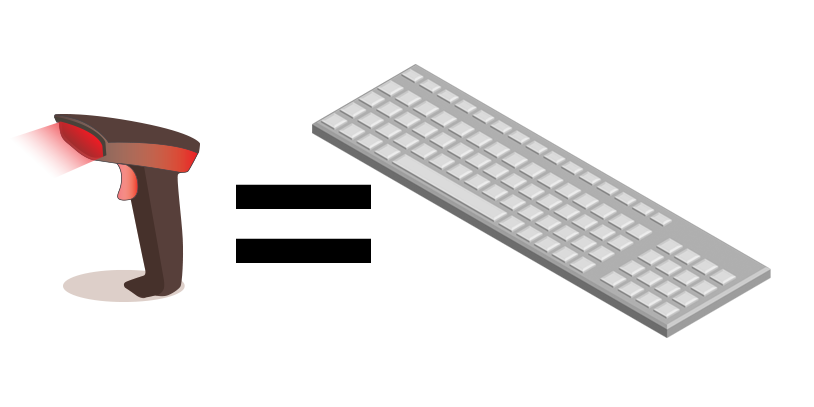
In years past, technology was different. We primarily used an RS232 connection for barcode scanners. Today, most barcode scanners connect via USB. This opens the door to a rising threat since barcode scanners now function as a second keyboard to a computer.
Additionally, barcode symbologies were not as advanced as they are today. Older linear codes cannot contain much data, but the newer 2D barcodes (Data Matrix, PDF417, QR, Aztec) can easily enable 50 to 70 ASCII characters.
Searching for In-Depth Information on this Security Threat?
We are very proud to introduce a comprehensive white paper on this subject providing more depth on the risks, responsibilities, costs, and remedies to this barcode security threat. Download our free white paper to learn more.
Inside the paper you’ll find information about:
✓ Why Data Security is an Ever-Present Issue
✓ How Cybercriminals Access Your System and Data
✓ Results of an OS System Takedown & General IT Mayhem
✓ Methods for Preventing Barcode Cyber Attacks
Put your barcode scanners to the test right now! Scan one of these 2D Data Matrix codes to find out how secure your barcode scanner really is.
What Is the Danger of a Security Threat?
Would you invite a cybercriminal to use your keyboard? Of course not! Now imagine scanning a barcode created by a cybercriminal with embedded Windows system control commands that can disable your firewall, delete files, auto-email, or even ping a system to provide hackers your IP address.
It’s as if the malicious barcode creates an open door to allow access to your keyboard. All it takes is an errant command beginning with the Open Windows Run Command, and a hacker can do his dirty work by accessing your computer keyboard as a secondary keyboard. Consider the damage a cyberthief could inflict with about 50 keystrokes to access to your operating system. Yikes!
It’s a fact—Malicious barcodes present a serious problem to all computer users with USB connected barcode scanners. As Hyperchem Ma demonstrated in his discussion at the PanSec conference in Tokyo, as keyboard emulation devices, unprotected barcode scanners can be taken over by hackers.
The hackers can create automatic and advanced system-wide attacks, using ASCII control characters, dialog attacks, and ADF (Advanced Data Formatting) embedded in the barcode.
Malicious operating system commands that lie hidden within barcodes are costly to fix because they wreak havoc with the data in your entire system. A rogue security breach could cause your system firewall to shut off, corrupt and delete files, and increase the susceptibility to future hacks through open port vulnerabilities. At the very worst, rogue barcodes are known to create government intelligence breaches and wipe out computer systems and network folders.
Consider how easily a “Rubber Ducky” can penetrate an operating system. This USB device looks like a normal thumb-drive, but it pretends to be a keyboard when inserted into a computer’s USB port. It can be programmed to type commands and take over the computer and an entire network. In just 15 seconds, a Rubber Ducky can destroy an operating system without detection.
A USB connected barcode scanner can read a 2D barcode programmed with a “payload” to act in the same manner as the Rubber Ducky.
The results of a system takedown by a malicious barcode are devastating. The expenses involve the cost of rebuilding, the cost of removing the potential for future threats, plus the loss of production time and profits.
Barcode Security Threats Also Create Mayhem for IT
In addition to the range of cybersecurity issues presented by today’s barcode security threat, it’s possible that these barcode issues may result in lost efficiency, lost time, and lost profits when chasing down potential threats and strange occurrences by staff. An internal response assessment is recommended, and a formal internal investigation may be necessary, depending upon the extent and impact on your critical business functions. Your company may also accrue sizeable additional costs if legal counsel is necessary for a sensitive data breach.
Recovering from a cyber attack requires more than bringing compromised systems back online and retrieving and updating lost data. Identifying and eliminating vulnerabilities becomes your IT department’s priority.
Are you prepared to make a substantial investment in these damage control measures, when investing in avoidance measures come at a comparatively minor cost?
How To Avoid the Fallout from a Malicious Barcode Security Breach
Here at ID Integration, we pride ourselves on being at the forefront of cutting-edge technology. Our innovations in marking, labeling, and validation speed you through compliance. They also save you money by preventing security threats.
We believe in the adage, “An ounce of prevention is worth a pound of cure.” Ensure good data with BarCodeOS® enabled scanners, the world’s only barcode readers equipped with FIREWALL technology: (The BarCodeOS® Security Filter is Patented)
✓ Avoid malicious operating system commands embedded in free form QR, PDF417, and Data Matrix symbologies. Dodge threats that are not limited to Windows operating systems.
✓ Use audible alarms to quickly recognize invalid syntax in barcodes and remove the chance for human error in validation. With one beep, you’ll know that the scanned barcode is good to go. Four beeps will signal an invalid syntax barcode.
✓ Scan anything containing a malicious command, and it will be stopped in its tracks—you’ll simply see “rogue barcode disabled” on the scanner display. BarCodeOS® technology contains a security filter that blocks dangerous run commands completely. BarCodeOS® will not allow this security filter to be disabled or reconfigured – making BarCodeOS® enabled scanners the world’s most secure hardware platform available today.
Don’t operate with the mistaken assumption that your barcodes will pass compliance when you don’t have the insurance of firewall protection. How can you be certain that you have good data when barcode readers are easily corrupted by malicious barcodes?
An ounce of prevention skirts the possibility of costly, extensive damage. Tackling this issue sooner, rather than later, and implementing corrections, saves untold sums of money. It’s following the 1-10-100 Rule, developed in 1992 by George Labovits and YSang Chang to describe efficiency. The costs of failures, when assuming data is correct when it is not, can be 100-fold compared to the cost of simply implementing procedures to prevent a breach in the first place.
Prevention is simple with BarCodeOS® enabled scanners. BarCodeOS® technology has applications for all industries:
Government compliance for FDA UDI labels to track the safety and recall of devices
Government compliance for the tracking of US DOD IUID parts
Hospital use to ensure patients receive the correct medications on schedule
Retail use going beyond inventory analysis—Retailers now receive information about shipments before they arrive
Barcode identity cards perform security checks in restricted facilities. Additionally, they monitor attendance of employees
Barcodes on boarding passes can be sent to cell phones to enable ticketless boarding
and many more industrial applications
BarCodeOS® enabled scanners improve productivity, asset management, error detection, and business intelligence. Use guaranteed firewall protection for peace of mind for your business management and analysis. Ensure that your awareness of product availability and inventory movement is sound. Make strategic decisions based on good data.
With our exclusive BarCodeOS® enabled scanners, there is no room for a security threat. Contact our experts at 425-438-2533 to adapt BarCodeOS® technology firewall protection for your barcoding applications.